-
Charly Castes and Andrew Baumann.
Sharing is leaking: blocking transient-execution attacks with core-gapped confidential VMs.
In Proc. 29th ACM International Conference on Architectural Support for Programming Languages and Operating Systems, Volume 4 (ASPLOS), La Jolla, CA, USA, June 2024.
-
Ziqiao Zhou, Yizhou Shan, Weidong Cui, Xinyang Ge, Marcus Peinado, and Andrew Baumann.
Core slicing: closing the gap between leaky confidential VMs and bare-metal cloud.
In Proc. 17th USENIX Symposium on Operating Systems Design and Implementation (OSDI), Boston, MA, USA, July 2023.
-
Meni Orenbach, Andrew Baumann, and Mark Silberstein.
Autarky: Closing controlled channels with self-paging enclaves.
In Proc. 15th European Conference on Computer Systems (EuroSys), Heraklion, Greece, April 2020. ACM.
-
Luke Nelson, James Bornholt, Ronghui Gu, Andrew Baumann, Emina Torlak, and Xi Wang.
Scaling symbolic evaluation for automated verification of systems code with Serval.
In Proc. 27th Symposium on Operating Systems Principles (SOSP), pages 225—242, Huntsville, Ontario, Canada, October
2019. ACM.
Best paper award, Distinguished artifact award.
-
Andrew Ferraiuolo, Andrew Baumann, Chris Hawblitzel, and Bryan Parno.
Komodo: Using verification to disentangle secure-enclave hardware from software.
In Proc. 26th Symposium on Operating Systems Principles (SOSP), pages 287—305, Shanghai, China, October 2017. ACM.
-
Jacob R. Lorch, Andrew Baumann, Lisa Glendenning, Dutch Meyer, and Andrew Warfield.
Tardigrade: Leveraging lightweight virtual machines to easily and efficiently construct fault-tolerant services.
In Proc. 12th Symposium on Networked Systems Design and Implementation (NSDI), pages 575—588, Oakland, CA, USA, May
2015.
-
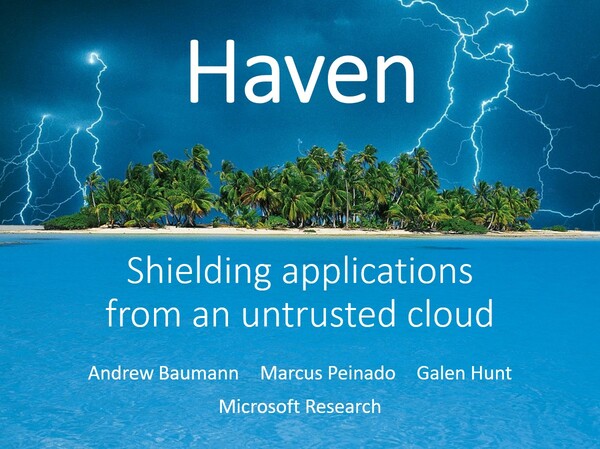
Andrew Baumann, Marcus Peinado, and Galen Hunt.
Shielding applications from an untrusted cloud with Haven.
In Proc. 11th Symposium on Operating Systems Design and Implementation (OSDI), Broomfield, CO, USA, October 2014.
Best paper award.
-
Andrew Baumann, Chris Hawblitzel, Kornilios Kourtis, Tim Harris, and Timothy Roscoe.
Cosh: clear OS data sharing in an incoherent world.
In Conference on Timely Results in Operating Systems (TRIOS), Broomfield, CO, USA, October 2014. ACM.
-
Andrew Baumann, Dongyoon Lee, Pedro Fonseca, Lisa Glendenning, Jacob R. Lorch, Barry Bond, Reuben Olinsky, and Galen C. Hunt.
Composing OS extensions safely and efficiently with Bascule.
In Proc. 8th European Conference on Computer Systems (EuroSys), pages 239—252, Prague, Czech Republic, April 2013.
ACM.
-
Adrian Schüpbach, Andrew Baumann, Timothy Roscoe, and Simon Peter.
A declarative language approach to device configuration.
In Proc. 16th International Conference on Architectural Support for Programming Languages and Operating Systems (ASPLOS).
ACM, March 2011.
-
Qin Yin, Adrian Schüpbach, Justin Cappos, Andrew Baumann, and Timothy Roscoe.
Rhizoma: a runtime for self-deploying, self-managing overlays.
In Proc. ACM/IFIP/USENIX 10th International Middleware Conference, Urbana Champaign, IL, USA, November 2009.
-
Andrew Baumann, Paul Barham, Pierre-Evariste Dagand, Tim Harris, Rebecca Isaacs, Simon Peter, Timothy Roscoe, Adrian Schüpbach, and Akhilesh Singhania.
The multikernel: A new OS architecture for scalable multicore systems.
In Proc. 22nd Symposium on Operating Systems Principles (SOSP), pages 29—44, Big Sky, MT, USA, October 2009. ACM.
SIGOPS Hall of Fame award, 2020.
-
Simon Peter, Andrew Baumann, Timothy Roscoe, Paul Barham, and Rebecca Isaacs.
30 seconds is not enough! A study of operating system timer usage.
In Proc. 3rd European Conference on Computer Systems (EuroSys), pages 205—218, Glasgow, Scotland, UK, April 2008.
ACM.
-
Andrew Baumann, Jonathan Appavoo, Robert W. Wisniewski, Dilma Da Silva, Orran Krieger, and Gernot Heiser.
Reboots are for hardware: Challenges and solutions to updating an operating system on the fly.
In Proc. USENIX Annual Technical Conference (ATC), pages 337—350, Santa Clara, CA, USA, June 2007.
-
Andrew Baumann, Gernot Heiser, Jonathan Appavoo, Dilma Da Silva, Orran Krieger, Robert W. Wisniewski, and Jeremy Kerr.
Providing dynamic update in an operating system.
In Proc. USENIX Annual Technical Conference (ATC), pages 279—291, Anaheim, CA, USA, April 2005.
-
Andrew Baumann, Jeremy Kerr, Jonathan Appavoo, Dilma Da Silva, Orran Krieger, and Robert W. Wisniewski.
Module hot-swapping for dynamic update and reconfiguration in K42.
In Proc. 6th Linux.Conf.Au, Canberra, Australia, April 2005.
-
Andrew Baumann, Jonathan Appavoo, Orran Krieger, and Timothy Roscoe.
A fork() in the road.
In Proc. 17th Workshop on Hot Topics in Operating Systems (HotOS), pages 14—22, Bertinoro, Italy, May 2019. ACM.
-
Andrew Baumann.
Hardware is the new software.
In Proc. 16th Workshop on Hot Topics in Operating Systems (HotOS), pages 132—137, Whistler, BC, Canada, May 2017.
ACM.
-
Jeffrey C. Mogul, Andrew Baumann, Timothy Roscoe, and Livio Soares.
Mind the gap: Reconnecting architecture and os research.
In Proc. 13th Workshop on Hot Topics in Operating Systems (HotOS). Usenix, May 2011.
-
Simon Peter, Adrian Schüpbach, Paul Barham, Andrew Baumann, Rebecca Isaacs, Tim Harris, and Timothy Roscoe.
Design principles for end-to-end multicore schedulers.
In Proc. 2nd Workshop on Hot Topics in Parallelism (HotPar), Berkeley, CA, USA, June 2010.
-
Pierre-Evariste Dagand, Andrew Baumann, and Timothy Roscoe.
Filet-o-Fish: Practical and dependable domain-specific languages for OS development.
In Proc. 5th Workshop on Programming Languages and Operating Systems (PLOS), Big Sky, MT, USA, October 2009.
-
Andrew Baumann, Simon Peter, Adrian Schüpbach, Akhilesh Singhania, Timothy Roscoe, Paul Barham, and Rebecca Isaacs.
Your computer is already a distributed system. Why isn't your OS?
In Proc. 12th Workshop on Hot Topics in Operating Systems (HotOS), Monte Verità, Switzerland, May 2009.
-
Qin Yin, Justin Cappos, Andrew Baumann, and Timothy Roscoe.
Dependable self-hosting distributed systems using constraints.
In Proc. 4th Workshop on Hot Topics in System Dependability (HotDep), San Diego, CA, USA, December 2008.
-
Adrian Schüpbach, Simon Peter, Andrew Baumann, Timothy Roscoe, Paul Barham, Tim Harris, and Rebecca Isaacs.
Embracing diversity in the Barrelfish manycore operating system.
In Proc. Workshop on Managed Many-Core Systems (MMCS), Boston, MA, USA, June 2008.
-
Andrew Baumann, Jonathan Appavoo, Dilma Da Silva, Orran Krieger, and Robert W. Wisniewski.
Improving operating system availability with dynamic update.
In Proc. Workshop on Operating System and Architectural Support for the On-Demand IT Infrastructure (OASIS), Boston, MA,
USA, October 2004.